Due to the performance nature of modern cloud-native applications, Kubernetes environments need to be highly distributed. Proper multi-cluster management and governance ensure consistent, secure operations across all environments. In this Refcard, we further explore Kubernetes multi-cluster management and governance, why it’s important, and core practices for success.
Source de l’article sur DZONE
Articles
Nowadays, most medical providers across the globe tend to implement cloud-based architecture for their medical services. And it’s not surprising, especially considering today’s pandemic reality; medical software is a must. However, to build a highly secure solution to deliver medical services, you must abide by the US 1996 law, namely the HIPAA Security Rule. This legislation represents a set of required and adequate protections for managing electronic confidential patient information and avoiding its disclosure without prior patient’s knowledge and even consent.
So, if you want to develop a medical solution and make your healthcare services cloud-based, you will have to apply the latest technologies for maintaining data compliance. To build cloud-based apps according to the Privacy Rule, most healthcare providers apply Amazon Web Services (AWS) due to its increased agility, security, and innovation potential.
 It’s never been easier to set up an ecommerce store and start selling. There are a dizzying array of ecommerce solutions available in 2021, and most are feature-rich and competitively priced.
It’s never been easier to set up an ecommerce store and start selling. There are a dizzying array of ecommerce solutions available in 2021, and most are feature-rich and competitively priced.
Ecommerce sites are notoriously difficult to migrate from platform to platform, so more often than not, you’ll be committed to your chosen solution for years. The key when choosing an ecommerce solution to maximize your return on investment, is to consider not just what your business needs today but what it will need tomorrow.
There are two basic approaches to ecommerce. The first is a dedicated platform that handles everything. The second is a plugin that adds ecommerce features to an existing CMS. Both approaches have benefits and drawbacks.
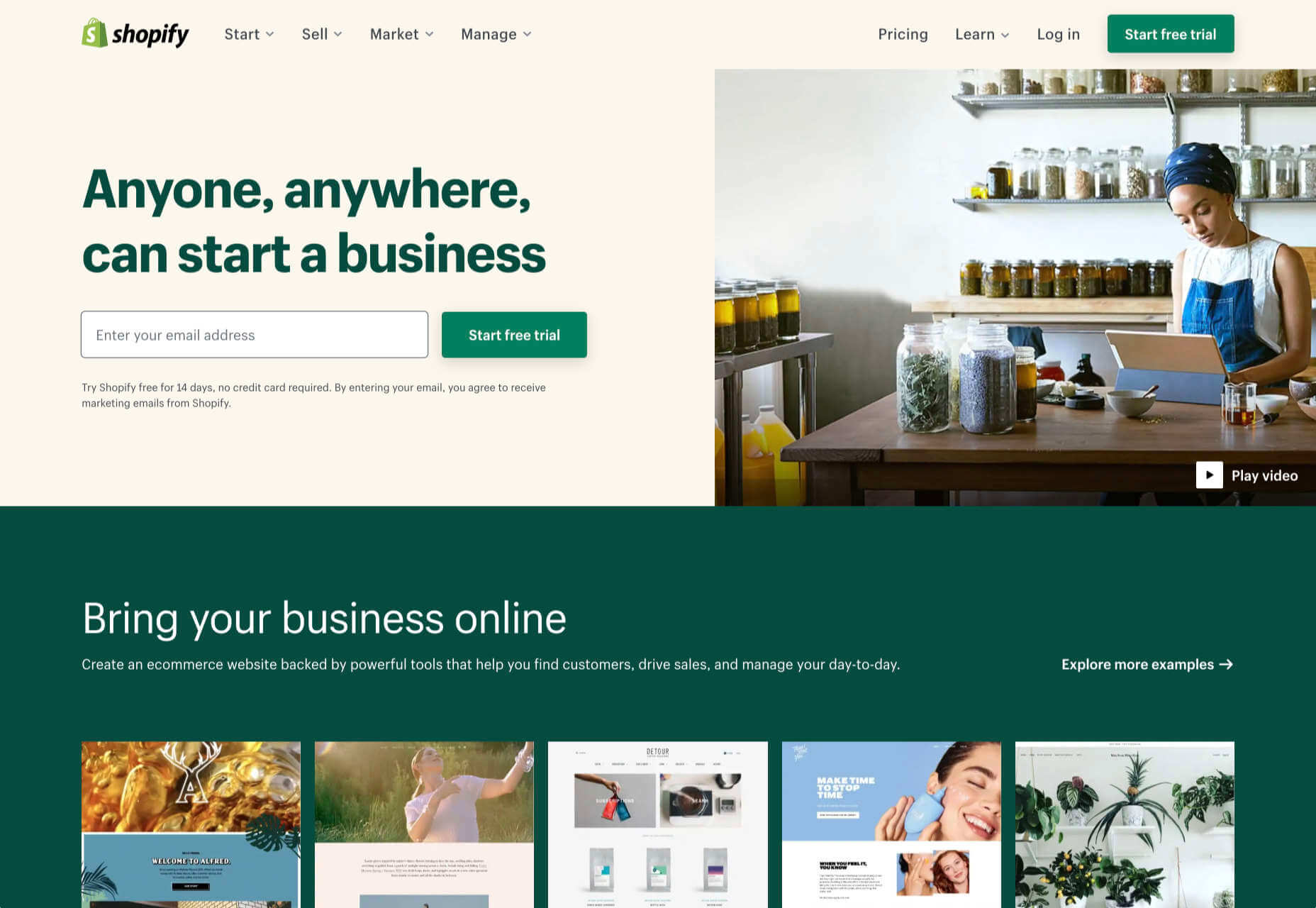
1. Shopify: Best for Almost Everyone
Shopify is a well-known, well-liked, and reliable dedicated ecommerce platform. As a system for getting a business off the ground and selling fast, it is peerless.
Shopify jealously guards developer access, with templates and plugins pre-vetted. Unlike some marketplaces, you can be confident that there are no hidden surprises in your shiny new store.
And because Shopify has passed the point of market saturation, it’s worthwhile for big players to provide their own plugins; credit services like Klarna and shipping companies like netParcel can be integrated with a few clicks.
The admin panel is a touch complex, as Shopify is designed to allow a single account to be linked to multiple stores. But once you’re set up and familiar with where to find everything, it’s a slick, streamlined business management system.
Whenever a client says, “we want to start selling online.” My first thought is, “Shopify.” And for 90% of clients, it’s the right choice.
And that’s where this roundup should end…except there’s still that 10% because Shopify isn’t perfect.
For a start, an all-in-one platform doesn’t suit everyone. If you already have a website you’re happy with, you’ll either need to migrate or lease a dedicated domain for your store.
Shopify’s platform is very secure, which inspires confidence in buyers, but the price of that security is a lack of flexibility in the design.
Then there’s the infamous variant limit. Shopify allows 100 variants on a product. Almost every client runs into that wall at some point. Let’s say you’re selling a T-shirt: male and female cuts are two variants; now add long or short sleeves, that’s four variants; now add seven sizes from XXS to XXL, that’s 28 variants; if you have more than three color options, you’ve passed the 100 variant limit. There are plugins that will allow you to side-step this issue, but they’re a messy hack that hampers UX for both customer and business.
Shopify should certainly be on every new store owner’s shortlist, but there are other options.
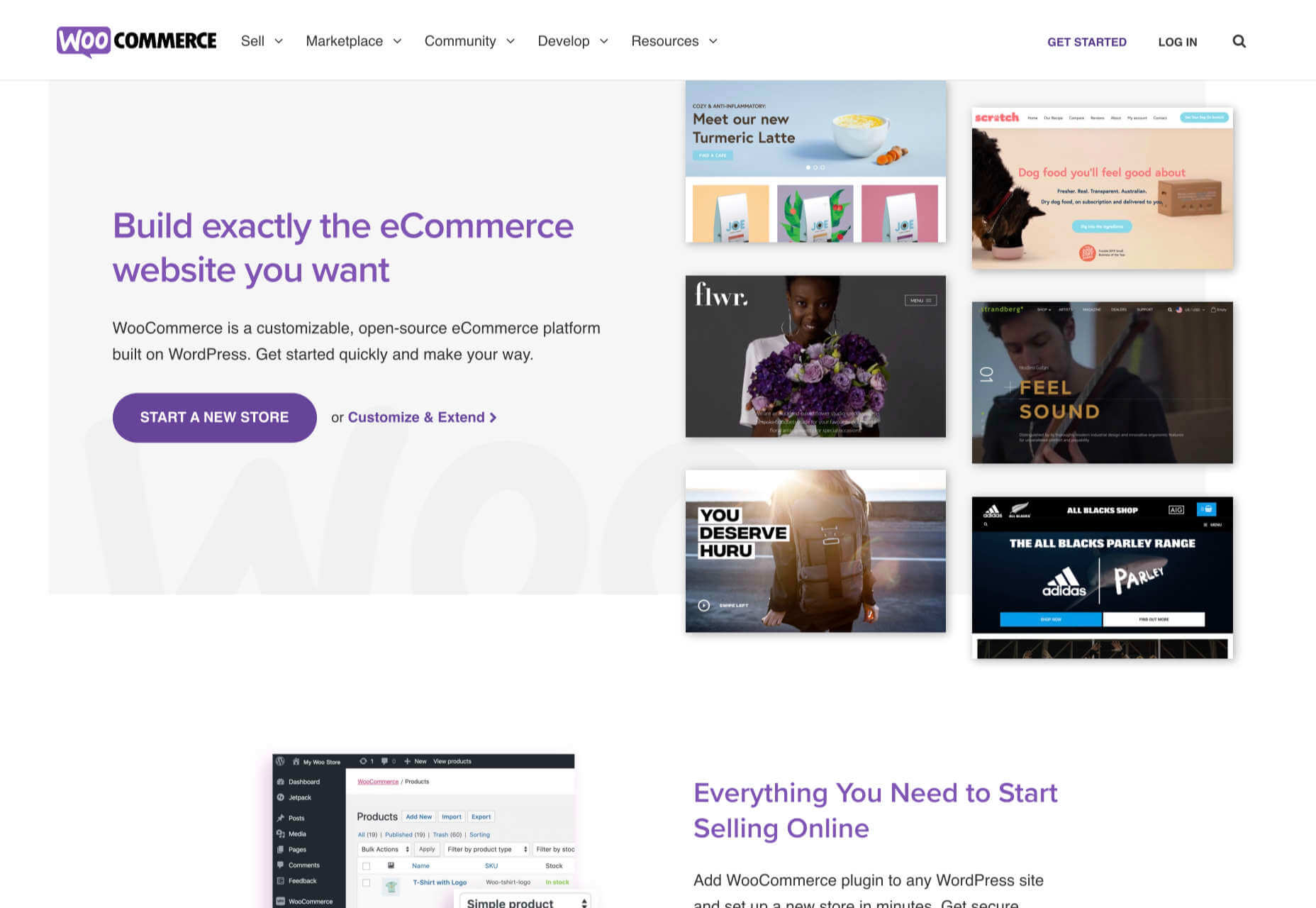
2. WooCommerce: Best for WordPress Users
If you’re one of the millions of businesses with a pre-existing site built on WordPress, then adapting it with a plugin is the fastest way to get up and running with ecommerce.
WooCommerce is regularly recommended as “Best for WordPress Users,” which is a back-handed compliment that belies the fact that WooCommerce reportedly powers 30% of all ecommerce stores. If running with the crowd appeals to you — and if you’re using WordPress, it presumably does — then you’re in the right place.
WordPress has a gargantuan plugin range. As such, there are other plugins that will allow you to sell through a WordPress site. The principle benefit of WooCommerce is that as the largest provider, most other plugins and themes are thoroughly tested with it for compatibility issues; most professional WordPress add-ons will tell you if they’re compatible with WooCommerce. If your business is benefitting from leveraging WordPress’ unrivaled ecosystem, it can continue to do so with WooCommerce.
The downside to WooCommerce is that you’re working in the same dashboard as the CMS that runs your content. That can quickly become unmanageable.
WooCommerce also struggles as inventories grow — every product added will slow things a little — it’s ideally suited to small stores selling a few items for supplementary income.
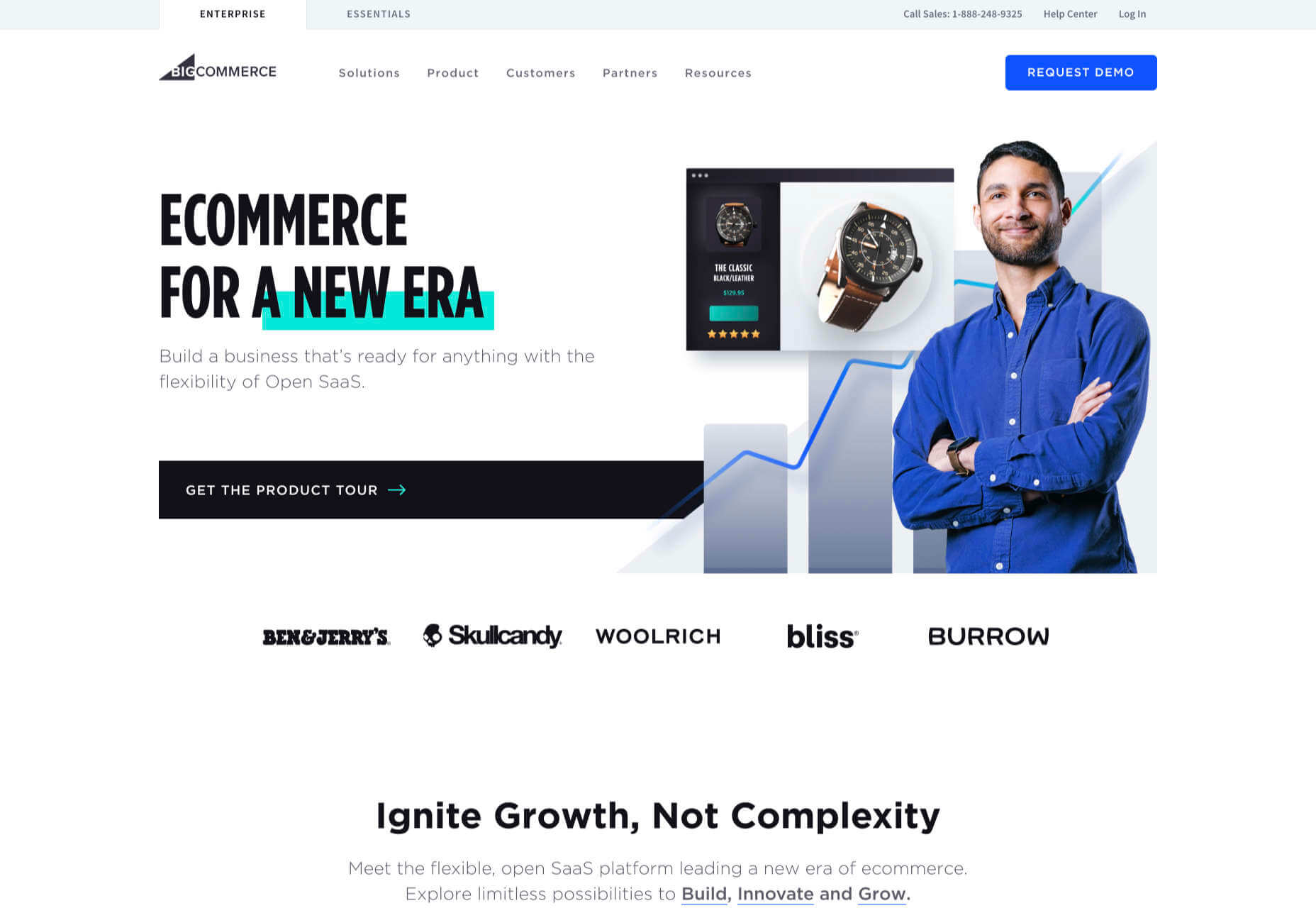
3. BigCommerce: Best for Growth
BigCommerce is an ecommerce platform similar to Shopify, but whereas Shopify is geared towards newer stores, BigCommerce caters to established businesses with larger turnovers.
The same pros and cons of a dedicated ecommerce solution that applied to Shopify also apply to BigCommerce. One of the considerable downsides is that you have less control over your front-end code. This means that you’re swapping short-term convenience for long-term performance. Templates, themes, and plugins — regardless of the platform they’re tied to — typically take 18 months to catch up with best practices, leaving you trailing behind competitors.
BigCommerce addresses this shortcoming with something Shopify does not: a headless option. A headless ecommerce platform is effectively a dedicated API for your own store.
Enabling a headless approach means that BigCommerce can be integrated anywhere, on any technology stack you prefer. And yes, that includes WordPress. What’s more, being headless means you can easily migrate your frontend without rebuilding your backend.
BigCommerce also provides BigCommerce Essentials, which is aimed at entry-level stores. It’s a good way to get your feet wet, but it’s not BigCommerce’s real strength.
If you have the anticipated turnover to justify BigCommerce, it’s a flexible and robust choice that you won’t have to reconsider for years.
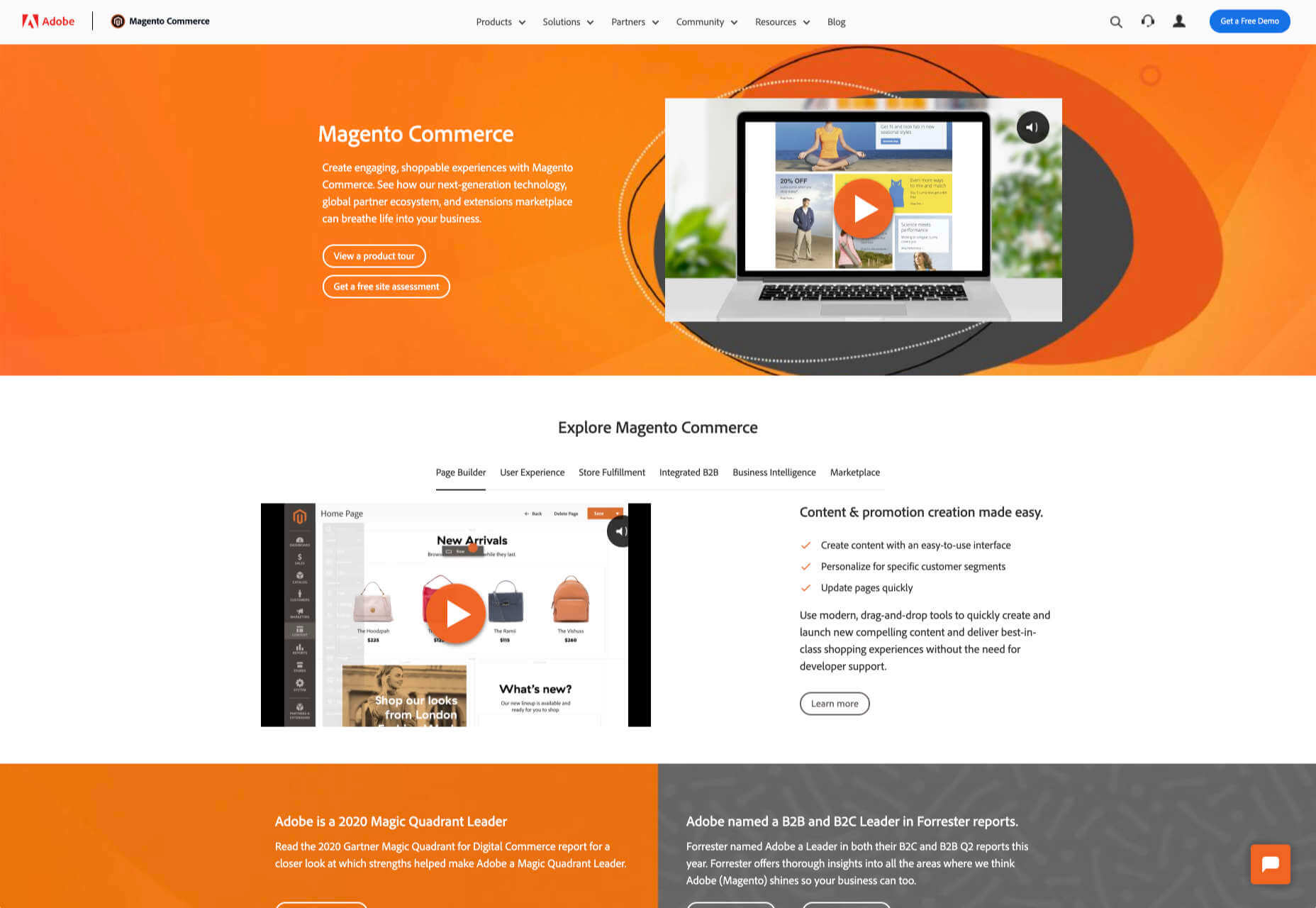
4. Magento: Best for Burning Budgets
If you have a development team at your disposal and a healthy budget to throw at your new store, then Magento could be the option for you.
You can do almost anything with a Magento store; it excels at custom solutions.
Magento’s main offering is its enterprise-level solution. You’ll have to approach a sales rep for a quote — yep, if you have to ask the price, you probably can’t afford it. Magento has the track-record and the client list to appeal to boards of directors for whom a 15-strong development team is a footnote in their budget.
That’s not to say that a Magento store has to be expensive; Magento even offers a free open source option. But if you’re not heavily investing in a custom solution, you’re not leveraging the platform’s key strengths.
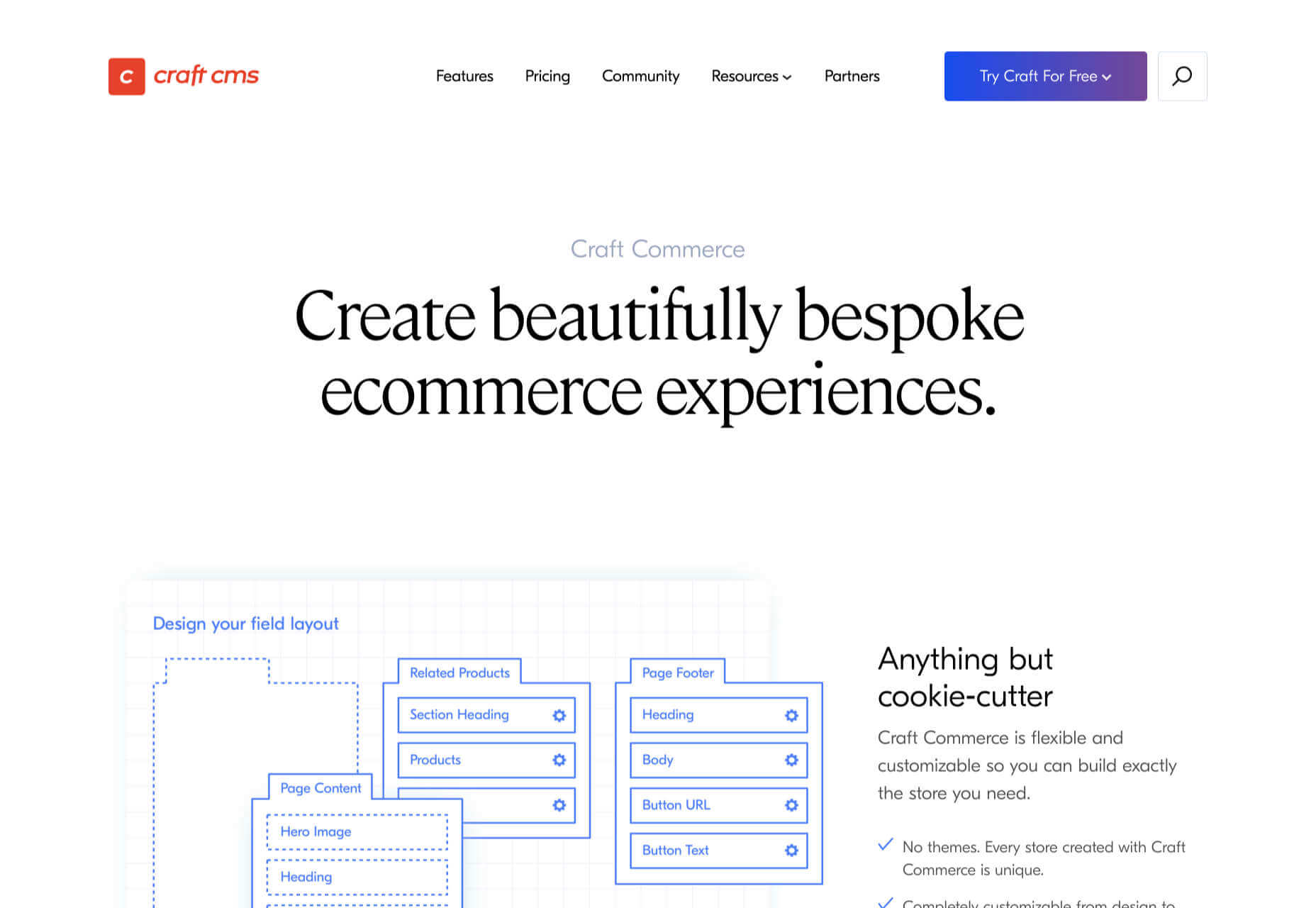
5. Craft Commerce: Best for Custom Solutions
If you’re in the market for a custom solution, and you don’t have the budget for something like Magento, then Craft Commerce is ideally positioned.
Like WooCommerce for WordPress, Craft Commerce is a plugin for Craft CMS that transforms it into an ecommerce store.
Unlike WordPress, Craft CMS doesn’t have a theme feature. Every Craft Commerce store is custom built using a simple templating language called Twig. The main benefit of the approach is that bespoke solutions are fast and relatively cheap to produce, with none of the code bloat of platforms or WordPress.
Because your site is custom coded, you have complete control over your frontend, allowing you to iterate UX and SEO.
You will need a Craft developer to set up Craft Commerce because the learning curve is steeper than a CMS like WordPress. However, once you’re setup, Craft sites are among the simplest to own and manage.
6. Stripe: Best for Outliers
Ecommerce solutions market themselves on different strengths, but the nature of design patterns means they almost all follow a similar customer journey: search for an item, add the item to a cart, review the cart, checkout. Like any business, they want to maximize their market share, which means delivering a solution that caters to the most common business models.
Occasionally a project happens along that doesn’t fit that business model. Perhaps you’re selling a product that’s uniquely priced for each customer. Perhaps you’re selling by auction. Perhaps you don’t want to bill the customer until a certain point in the future.
Whatever your reason, the greatest customization level — breaking out of the standard ecommerce journey — can be managed with direct integration with Stripe.
Stripe is a powerful payment processor that handles the actual financial transaction for numerous ecommerce solutions. Developers love Stripe; its API is excellent, it’s documentation is a joy, it’s a powerful system rendered usable by relentless iteration.
However, this approach is not for the faint-hearted. This is a completely custom build. Nothing is provided except for the financial transaction itself. Every aspect of your site will need to be built from scratch, which means hefty development costs before seeing any return on investment.
The Best eCommerce Solution in 2021
The best ecommerce solution is defined by three factors: the size of your store, the anticipated growth, and the degree of custom design and features you want or need.
Shopify is the choice of most successful small stores because you can be selling inside a day. For businesses with an existing presence and a smaller turnover, those on WordPress will be happy with WooCommerce. For larger stores planning long-term growth, BigCommerce’s headless option is ideal. Craft Commerce is a solid performer that marries low costs with flexibility for businesses that need a custom approach.
Featured image via Unsplash.
The post 6 Best Ecommerce Solutions for 2021 first appeared on Webdesigner Depot.
Internal APIs are designed primarily to streamline software development and simplify systems and operational processes. These currently represent the vast majority of use cases.
Internal APIs are often overlooked since they are aimed at in-house developers. These types of APIs generally work with proprietary data specific to a company and its departments. Although this data must be protected, it must also be accessible to those who work with it. Internal APIs allow for exactly this kind of secure access, creating more efficient development cycles for their products.
Here at ShiftLeft, we are gearing up for Shifting Left: ’21, a one-day application security conference for developers and security practitioners on Jan 28, 2021. I’ve been a huge fan of security conferences ever since I attended my first security conference, NorthSec in Montreal. This time, I am excited to be on the organizer’s side and present this conference to you.
Shifting Left: ‘21 is entirely online and free to register here. Now let’s get into it! Here are the sessions that I am most excited about and that you should attend if you like machine learning, developing secure applications, or hacking into applications.
 Every week users submit a lot of interesting stuff on our sister site Webdesigner News, highlighting great content from around the web that can be of interest to web designers.
Every week users submit a lot of interesting stuff on our sister site Webdesigner News, highlighting great content from around the web that can be of interest to web designers.
The best way to keep track of all the great stories and news being posted is simply to check out the Webdesigner News site, however, in case you missed some here’s a quick and useful compilation of the most popular designer news that we curated from the past week.
Sidekick Browser – The Fastest Browser Built for Work
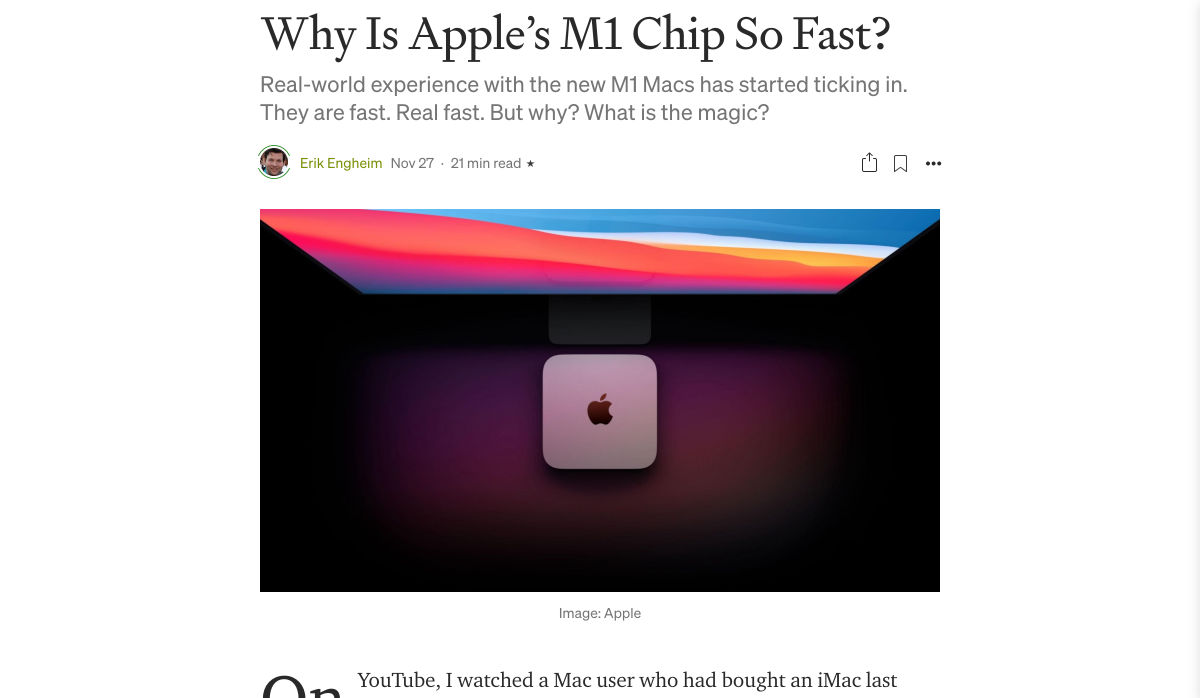
Why is Apple’s M1 Chip so Fast?
Two Color Combinations – A Curated Collection of 164 Two-color Palette Combinations
5 Tips to Build a Stunning Website that Stands Out from the Crowd
10+ Bootstrap Newsletters
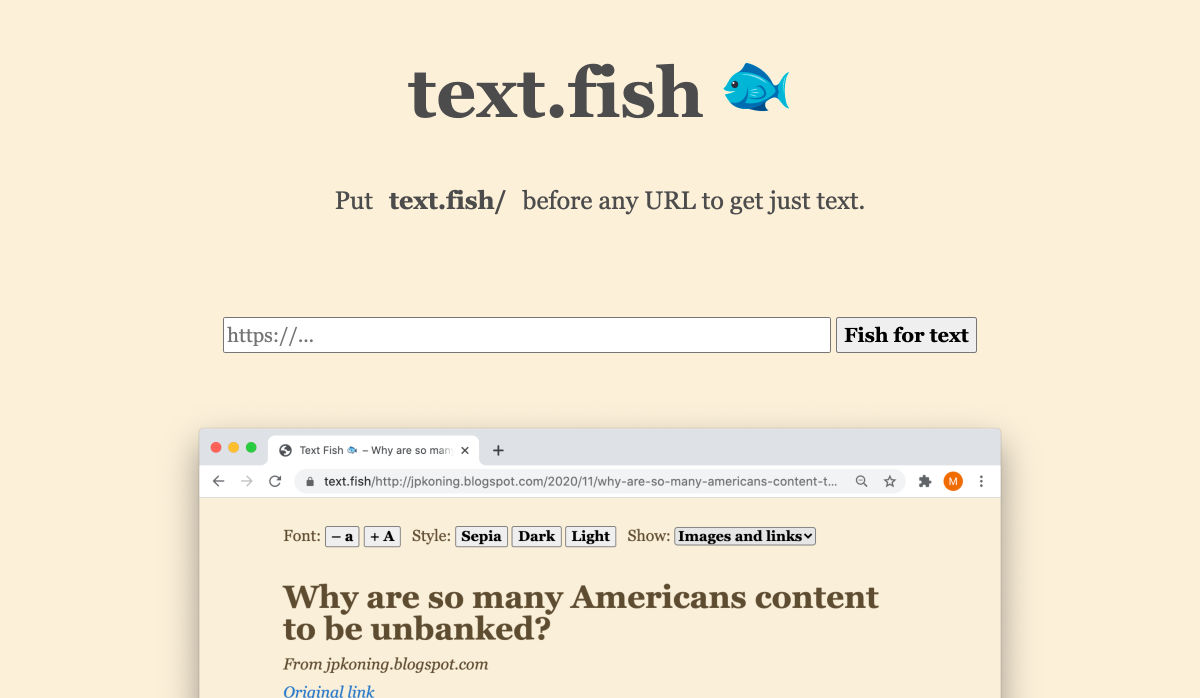
Text Fish – Get Just Text
Ecommerce Website Designs: 27 Best Online Shops and Why They Work
SpaceHey – MySpace Reborn
State of CSS – 2020
5 Overlooked Mobile Experience Design Best Practices
Modern Blackletter Inspired Fonts and their Use in Web Design
Internxt Drive – Secure & Private Cloud Storage Service
Spline – 3D for the Web (Preview Release)
Nots – A Free Beautifully Designed Note-taking App for your Desktop
Google Play’s Best of 2020
Beacon – Run SQL Commands in Slack
Designing for the New Reality: Getting Rid of Pre-COVID Assumptions
Undoing the Toxic Dogmatism of Digital Design
Color Theory: A Beginner’s Guide for Designers
Atkinson Hyperlegible Font
11 Tips for Creating a Usable Website Contact Page
The 7 Secrets to a Great Conversation
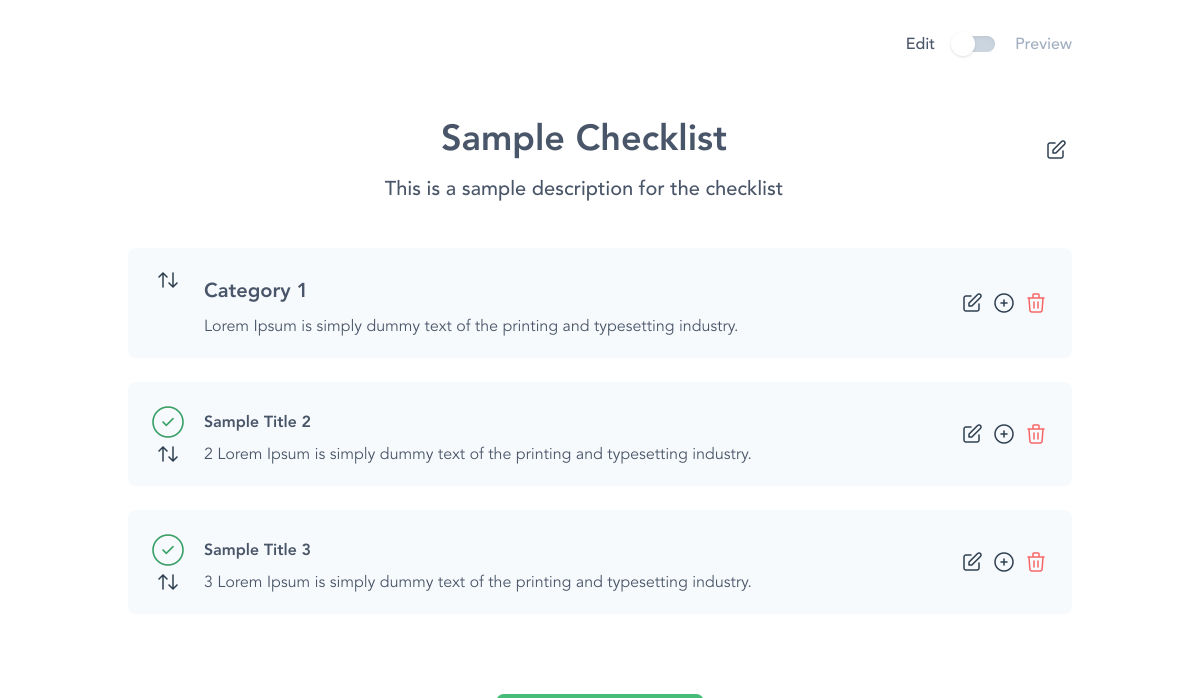
Checklist Generator – Create Checklists for Free and Host Them Wherever You Want
Empathetic Design: The First Stage of Design Thinking
Handy Guide to Networking for UX Designers
Want more? No problem! Keep track of top design news from around the web with Webdesigner News.
PDF documents are small-sized, highly secure files. Almost all businesses use PDFs for processing their files. The reason being a distinguishing feature of maintaining format regardless of the tool used to access PDF files. It’s no surprise that all our invoices, official documents, contractual documents, boarding pass, bank statements, etc. are usually in PDF format.
Even as developers, we come across scenarios when a PDF file needs to be verified or used to locate certain parts of data. You can either do this manually given that you have loads of time to spare or you opt for automation testing. When it comes to handling tricky components of such files using automation, it might seem a bit too tricky. But that’s not the case. Selenium test automation can make it really easy to test PDF file formats.
 A hacked WordPress site is as damaging as having your home burgled. It can completely shatter your peace of mind and adversely impact your online business.
A hacked WordPress site is as damaging as having your home burgled. It can completely shatter your peace of mind and adversely impact your online business.
Why do hackers target WordPress sites? The answer is relatively simple: WordPress is the single biggest platform for website creation these days, so there’s a larger base to attack; this attracts the attention of online criminals.
So, how can a hack impact your website?
Depending on the type of attack, your website could suffer any of the following:
- It could be defaced completely;
- It could load or operate very slowly on any device;
- It could completely crash and malfunction;
- It could display the dreadful “White Screen of Death”;
- Its incoming visitors could be redirected to other suspicious websites;
- It could lose all your valuable customer data.
This list is not exhaustive but you get the idea.
Now that we know how a successful hack can impact your website and online business, let us look at the top 10 reasons behind WP hacks and prevent them.
1. An Insecure Web Host
Like any website, WordPress is hosted on a web host or server. Unfortunately, most site owners do not pay much attention to the web host they select and choose the cheapest they can find. For example, it is more affordable to host a website on a shared hosting plan — one that shares its server resources with many other websites like yours.
This can make your site vulnerable to hackers as a successful hack into any website on the shared server. A single hacked site can consume the overall server bandwidth and impact all the other sites’ performance.
The only way to fix this problem is to opt for a reliable host and a virtual or dedicated server.
Pro tip: If you’re already using a shared hosting plan, check with your hosts if they offer VPS hosting and make the switch.
2. Use of Weak Passwords
Weak passwords are the main reason behind successful brute force attacks that target your account. Even to this day, users continue to use weak and common passwords like “password” or “123456”; if you’re one of them, your website could land in trouble!
Guessing weak passwords allows hackers to enter the admin accounts where they can inflict the maximum damage.
How do you fix this problem? Simple, ensure all your account users (including admin users) configure strong passwords for their login credentials. With at least 8 characters, passwords must be a mix of upper- and lower-case alphabets, numbers, and symbols.
For added safety, install a password management tool that can automatically generate and store strong passwords.
Pro tip: You can use a plugin to reset passwords for all your users.
3. An Outdated WP Version
Outdated software is among the most common reasons why websites get hacked. Despite being free to download, most site users defer updating their site to the latest version, for fears of updates causing their site to crash.
Hackers take advantage of any vulnerability or bug in an older version and cause issues like SQL Injections, WP-VCD Malware, SEO Spam & other major issues like website redirecting to another site.
How do you solve this problem? When you see a notification about an update on your dashboard, update your site as soon as possible.
Pro tip: If you are worried about updates crashing your live website, you can first test the updates on a staging site.
4. Outdated WP Plugins and Themes
Similar to the previous point, hackers also take advantage of outdated, unused, or abandoned plugins and themes installed on websites. With over 55,000 plugins and themes that are available, it is easy to install a plugin or theme, even from unsafe or untrusted websites.
Plus, many users do not update their installed plugins/themes to the latest version or do not find the updated version. This makes it easier for hackers to do their job & infect sites.
How do you avoid this problem? As with the core WP version, update each of your installed plugins/themes on your site regularly. Take stock of all the unused ones and remove them or replace them with better alternatives.
You can update your plugins/themes from your hosting account.
Pro tip: We suggest setting aside time every week to run updates. Test them on a staging site and then update your site.
5. Common Admin Usernames
In addition to weak passwords, users also create common usernames that are easy to guess.
This includes common usernames for admin users like – “admin”, “admin1”, or “admin123”. Common admin usernames make it easier for hackers to get into admin accounts and control backend files in your WP installation.
How do you avoid this problem? If you are using any such usernames that are easy to guess, change them immediately to a unique username. The easiest way of doing it is through your hosting account’s user management tool, by deleting the previous admin user and creating a new admin user with a unique username.
As the first step, change the default username of your admin user and limit users who have administrator privileges.
Pro tip: WordPress has 6 different user roles with limited permissions. Only grant admin access to users who really need it.
6. Use of Nulled Plugins/Themes
Coming back to the importance of plugins/themes, users have access to many websites that sell nulled or pirated copies of popular and paid plugins and themes. While these are free to use, they are often riddled with malware. They can compromise your website’s overall security and make it easier for hackers to exploit.
Being a pirated copy, nulled plugins/themes do not have any available updates from its development team, hence will not have any security fixes.
How do you fix this problem? Simple, for a start, only download original plugins and themes from trusted websites and marketplaces.
Pro tip: If you don’t wish to pay for paid or premium plugins and themes, opt for a free version of the same tools that will have limited features but are still safer to use than the nulled version.
7. Unprotected Access to wp-admin Folder
To take control of your site, hackers often try to break into and control your wp-admin folder in your installation. As the website owner, you must take measures to protect your wp-admin directory.
How can you protect your wp-admin folder? First, restrict the number of users having access to this critical folder. Additionally, apply for password protection as an added layer of security for access to the wp-admin folder. You can do this using the “Password Protection Directories” feature of the cPanel in your web host account.
Pro tip: Besides these fixes, you can also implement Two Factor Authentication (or 2FA) protection for all your admin accounts.
8. Non-SSL Website
You can easily migrate your HTTP website to HTTPS by installing an SSL certificate on your site. SSL (or Secure Socket Layer) is a secure mode of encrypting any data transmission between your web server and the client browser.
Without this encryption, hackers can intercept the data and steal it. Plus, a non-secure website can have many negative implications for your business – lower SEO ranking, loss of customer trust, or a drop in incoming traffic.
How do you fix this problem? You can quickly obtain an SSL certificate from your hosting company or SSL providers. It encrypts all data that is sent from and received by your website.
Pro tip: You can get a free SSL certificate from places like Let’s Encrypt, but these provide limit protection that will only be sufficient for a starter site or small site.
9. No Firewall Protection
Lack of firewall protection is another common reason why hackers can bypass website security measures and infiltrate the backend resources. Firewalls are the last line of defence against hackers and work like the security alarm installed on your house. Firewalls monitor web requests coming from various IP addresses, including the suspicious (or bad) ones.
They can identify and block requests that are known to be malicious in the past, thus preventing easy access for hackers to your website domain. Web application firewalls can thwart various attacks, including brute force attacks, XSS, and SQL injections.
Pro tip: A firewall provides much-needed security and is your first line of defence. But it’s important to also have a malware scanner installed.
10. Lack of WordPress Hardening Measures
Typically, hackers target the most vulnerable areas or weaknesses within a WP installation, to illegally access or damage the website. The WordPress team has identified these vulnerable areas and has devised a list of 12 hardening measures recommended for every website.
A few of these include:
- Disabling the File Editor;
- Preventing PHP execution in untrusted folders;
- Changing the security keys;
- Disallowing plugin installations;
- Automatic logout of inactive users;
How do you implement these hardening measures? While some steps are easy to understand, others require the technical expertise of how WordPress works.
Pro tip: You can implement hardening measures on your own. However, some measures require technical expertise so in these cases, it’s much easier and safer to use a plugin.
Featured image via Pexels.
 The transitioning of power is fraught with difficulties. Different teams have different values, different experience, different expertise, different priorities, and that leads to different tooling, and different methodologies.
The transitioning of power is fraught with difficulties. Different teams have different values, different experience, different expertise, different priorities, and that leads to different tooling, and different methodologies.
It’s tempting to think of web design as an end-to-end process, starting with research and concluding with metrics. The reality is that most designers and developers join projects part-way through an ongoing process.
That leaves us with a difficult choice: do we try and meet the client’s expectations with our own toolset, or adapt to the tools and processes that are already in place?
For anyone who’s taking over a web project from a different designer/developer/agency (D/D/A), here’s a practical guide to help you make a success of the transition.
Step 1: Find Out What Went Wrong
99.99% of the time, something broke down in the previous client-D/D/A relationship.
In my experience it’s almost never about money. Most clients are willing to pay above the basic market rate if they believe they’re receiving a good return on their investment. A client that tells you the previous D/D/A is simply too expensive is anticipating negotiating your fees.
happy clients don’t shop around
Occasionally you’ll find that a freelance designer has been headhunted by an agency, and is no longer available. Occasionally the company outgrows a D/D/A, moving into areas that the D/D/A doesn’t support. But these situations are rare, happy clients — even moderately content clients — don’t shop around. If they’re speaking to you, something motivated them to do so.
It is alarmingly common that a D/D/A simply goes AWOL. It’s most common at the lower end of the market where the sums of money involved are less likely to prompt a legal dispute. Frequently, an unreputable D/D/A will ghost a client in favour of a better, newer opportunity.
Sometimes the client hires a new manager, and the new manager ushers in revised expectations that the previous D/D/A can’t meet.
Most commonly, the previous D/D/A has dropped the ball one too many times — mistakes happen, and reasonable clients will tolerate them provided they are rectified promptly, but everyone has their limits.
Most clients will be more than happy to explain what went wrong in the previous relationship; it will inevitably be a one-sided explanation, but it will help you to understand the client’s expectations.
Be extremely wary of a client who doesn’t know what went wrong. Be even more wary of a client who talks about “upgrading” their outsourcing — they’re trying to flatter you. In these cases the client may well be hiding something — like their failure to pay invoices.
Remember: at some point the previous D/D/A was new, and excited about having a new client, was optimistic about the project, and it didn’t end well. The best way to not repeat mistakes is to learn from them, and to do that you need to know what they were.
Step 2: Carry Out a Comprehensive Audit
We’re often so eager to secure new work, that we rush to have the client sign on the dotted line, expecting to be able to tackle any problems later.
It is imperative that as a professional, you keep your promises. Before you make those promises, take your time to understand the project and related business. If a client is invested enough to sign a contract with you they won’t mind you doing due diligence first.
Is There Still a Relationship With the Previous Designer/Developer/Agency?
Clients rarely have a full picture of their project — they’re not web professionals, if they were they’d be building their own sites. Your best source of information is the previous D/D/A.
Before you contact the previous D/D/A check with your client; it’s possible they don’t know they’re being replaced yet. If your client is fine with it, then reach out.
When you speak to the previous D/D/A be sensitive to the fact that you’re taking money out of their pocket. Certainly the previous D/D/A may tell you where to go, they may ignore you altogether, but most will be pragmatic about handing over a project if only to ensure their final invoice to their now ex-client is paid promptly.
Every site has its idiosyncrasies, if you can establish a friendly rapport with the previous D/D/A then the transition will be considerably less bumpy.
Who Controls the Domain Name(s)?
In my opinion a company’s domain name(s) should always be held by the company; it’s such an essential business asset that it should be guarded as jealously as the company’s bank accounts.
Unfortunately there are businesses that outsource everything to do with the web. If the break with the previous D/D/A is acrimonious then securing the domain name could be problematic.
It’s not your job to secure the domain name — you have no leverage, the client does. It is your job to impress upon the client how mission-critical the domain name(s) is.
Who Controls the Hosting?
Hosting arrangements vary from project to project. It’s not uncommon, nor unreasonable, for the previous D/D/A to be hosting the client’s site on their own space. If that is the case, be prepared to migrate it quickly either to your own server, or a dedicated space.
If you’re migrating onto a new space pay particular attention to the email provision. Taking over a project usually means taking over a live project, and that usually means email accounts.
In any case, you need full access to the hosting space. You certainly need FTP access, you probably need SSH access.
In addition to hosting, check if your client’s site uses a CDN, and if it does, who has control of it.
Backend Source Code
Once you have FTP access to the hosting server you can probably grab all backend code from the server.
The benefit of grabbing the code from the server — as opposed to accepting files from the previous D/D/A — is that you can be absolutely certain you’re getting the current (working) code.
If the client has broken with the previous D/D/A because they were unable to deliver on a particular task, you do not want to be working with files that have been partially modified.
Fresh Installs
If you’re working with something like a CMS, it’s often a good idea to run a fresh install on your server, and then copy across any templates, plugins, and migrate the database.
Frontend Source Code
When it comes to acquiring source code, frontend code is far more problematic than backend.
frontend code is far more problematic than backend
If the previous D/D/A is even part-way competent then the CSS and JavaScript on the web space is minified. Minified CSS is not too problematic and can be unminified fairly easily, but you do not want to be unpicking a minified JavaScript file — I once had a project in which a developer had minified his own code in the same file with all of his dependencies, including both Vue and jQuery [yes, I know].
Dealing with frontend source code can take on an additional dimension if you discover that the previous D/D/A used techniques you don’t — using Less instead of Sass, or writing scripts in TypeScript.
Unminifying CSS & JavaScript
Unminifying (or beautifying, or prettifying) code is reasonably easy. There are tools online that will help, including Unminify, Online CSS Unminifier, FreeFormatter, JS Minify Unminify, and more. You’ll also find plenty of extensions for code editors including HTML-CSS-JS Prettify for Sublime Text, and Atom-Beautify for Atom. You’ll find that some editors have the functionality built in.
A word of warning: code beautification does not restore comments, and in the case of JavaScript, does not unobfuscate variable names. Beautifying code is no substitute for a copy of the original, unminified source code.
Emergency Measures
If unminifying the source code isn’t possible for any reason, or more likely, the unminified JavaScript still looks like minified code — albeit nicely formatted minified code — then your last resort is to import the code and override it where necessary.
The first thing to do in this case is to explain the situation to your client. Make sure they understand this is a temporary patch that you’ll iron-out as you rebuild parts of the project.
Then, copy and paste the old minified code into a fresh project setup. For CSS that probably means creating a legacy.scss file, including the old CSS, and importing it into your own Sass. For JavaScript, create a legacy.js file, add all the old JS, and import that.
This will result in a much bigger set of files than necessary, you may end up using !important in your style declarations [yuck], and you’ll trigger lots of Lighthouse warnings about surplus code.
However, in the likely event that your client has a long list of changes they wanted live yesterday, this dirty hack will give you a working site that you can then rebuild piece by piece over time.
Assets
Assets normally means images, and images can normally be grabbed via FTP.
Occasionally — although less occasionally now image files rarely contain text — you’ll need the source files to make changes to images.
Whether or not the client has them, or if the previous D/D/A will hand them over, depends largely on the agreement between the client and the previous D/D/A.
Most businesses are reasonably aware of the importance of brand assets, so you’ll probably find they at least have a copy of their logo; whether it’s an SVG or a JPG is another matter entirely. Impress upon them the importance of locating those files for you.
Third Party Code
It is rare to receive a project that doesn’t rely on third party code. That third party code is probably entwined in the custom source code, and unpicking it is a time-consuming job.
It is very likely the previous D/D/A used a library or framework, and given the increasing number of them, it’s even more likely that the library or framework they used is not the one you prefer.
Whether you choose to unpick the code and swap out the previous D/D/A’s dependencies for your own preferences (usually faster in the long term), or whether you choose to work with what you’re given (usually faster in the short term) is entirely up to you.
In my experience it’s no hardship to pick up another CSS library; switching from one JavaScript framework to another is a substantially bigger job involving not just syntax but core concepts.
Beware Build Environments
Everyone has their own way of doing things. Some D/D/As embrace build environments, some do not. Some build environments are simple to use, some are not. Some build environments are adaptable to your process, some are not.
Unlike adopting a library, or even a framework, adopting a new build process is rarely a good idea
Build environments are numerous — Gulp, Grunt, and Webpack are all popular — and D/D/As are almost as opinionated about them as they are about CMS.
In lieu of raw files, it’s not uncommon for the previous D/D/A to tell you to “just run such-and-such CLI” command, to match up your local environment to theirs. Unlike adopting a library, or even a framework, adopting a new build process is rarely a good idea because you’re relegating yourself from expert to novice at a time when you’ve yet to earn your new client’s trust.
Stand your ground. Their approach failed, that’s why you’ve been brought in. You do you.
Who is Licensed?
Any third part code that has been paid for is licensed. Always check who holds these licenses. As well as being legally required, valid licenses are normally required for updates, bug fixes, and in some cases support.
Common pitfalls include: font licenses (which may be licensed under the previous D/D/A’s Creative Cloud, Fontstand, Monotype, etc. account); stock image licenses (which may be licensed for use by the previous D/D/A alone); and plugins (which are frequently bulk-licensed to D/D/As in bundles).
It’s depressingly common to find clients using unlicensed assets. On more than one occasion I’ve had to explain to a client the potential consequences of using pirated fonts.
Fortunately it’s increasingly common for third party providers to attach a licence to a specified domain, which means you may be able to claim the licence on behalf of your client. Major suppliers like CMS and ecommerce solutions frequently have an option for the previous developer to release a licence and allow you to claim it.
In the case of licensing, if you’re unsure, do not be afraid to reach out to the third party provider and check with them if your client is licensed once they break ties with their previous D/D/A.
The only thing that sours a client relationship faster than telling them they need to buy a license they thought they’d already paid for, is telling them they’re being sued for copyright infringement.
Protect your client, and protect yourself, by making sure everything is licensed properly. If you can get something in writing to that effect from the previous D/D/A, do.
Who Has the Research and Analytics?
One of the major benefits of taking over a site, as opposed to building from scratch, is that you have a measurable set of site-specific data to guide your decision making.
This only applies if you have the data, so ask to be added to the client’s analytics account.
There’s a strong chance that the design research carried out by the previous D/D/A is considered an internal document, not a deliverable, by the previous D/D/A. Check with your client: if they paid for the research (is it specified on an invoice?) then they’re entitled to a copy.
We Have a Blog Too…
Clients have a tendency to use the term “website” as a catch-all term for everything digital.
When you take responsibility for a website, you’re almost always expected to take responsibility for any digital service the client uses. That means, newsletter services like Mailchimp, customer service accounts like Intercom, and 227,000 page WordPress blogs that they forgot to mention in the initial brief.
Repeat the whole of Step 2 for every additional app, micro-site, blog, and anything else the client has, unless you are expressly told by the client not to.
Step 3: The Point of No Return
Up until now, you haven’t asked the client to sign on the dotted line. This whole process is part of your due diligence.
By checking these things you can identify unforeseen problems, and potential costs. Are you tied to an obscure build process? Do you need to relicense the CMS? Do you need to recreate all of the site assets?
Some of these conversations are hard to have, but the time to have them is now
If there is any question of the project being more complex than anticipated, have an honest conversation with your client — they will appreciate your transparency, and they’ll appreciate being kept informed. Any client who doesn’t value a clear picture of what they’re paying you for, isn’t a client you want.
Some of these conversations are hard to have, but the time to have them is now, not three months down the line.
This is the point of no return. From this point on, any problems aren’t the previous D/D/A’s, they’re yours.
Change the Passwords
For every service you have, from the newsletter login, to the CMS login, to the FTP details, change the password. (Make sure you notify the client.)
Set Up a Staging Site
You’re going to need a staging site so your new client can preview the work you’ve done for them.
Set the staging site up immediately, before you’ve made any changes to the code. In doing so you’ll discover early on if there are files missing, or issues with the files you do have.
Successfully Transitioning a Project
When a client commissions a site from scratch they are filled with expectation. The fact that they are leaving their previous D/D/A and seeking you out demonstrates that their experience fell short of their hopes.
You now have a client with realistic — perhaps even pessimistic — expectations. You have a benchmark against which your work can be objectively measured.
When problems arise, as they invariably will, never try to blame the previous D/D/A; it was your job to assess the state of play before you started work. If there is an issue with legacy assets, you should have brought it to your client’s attention early on.
If you learn from the previous D/D/A’s mistakes, you won’t be handing the project on to someone else any time soon.
Featured image via Unsplash.
 When it comes to compliance, website developers need to keep their eyes on more than just ADA regulations and Section 508. Privacy laws are a big consideration and decisions on how to build privacy into a website start with architects.
When it comes to compliance, website developers need to keep their eyes on more than just ADA regulations and Section 508. Privacy laws are a big consideration and decisions on how to build privacy into a website start with architects.
And that’s exactly what website developers (and designers!) are. They build up attractive, functional websites and apps for their clients. Yes, they work closely with clients, copywriters, vendors, and other professionals to get the job done, but the developers are the ones who put it all together.
That’s why it’s critical that website developers are well-versed in marketing privacy laws — these regulations directly impact the end results of their work. But how does a website architect create a digital platform that honors both user privacy and the needs of their clients?
What Privacy Laws Are Important For Web Developers?
The two biggest privacy laws that web developers need to keep tabs on are the General Data Protection Regulations (GDPR) and the California Consumer Privacy Act (CCPA). Each law has its own unique scope and provisions, but they both shifted the landscape in defining an individual’s rights to their personal data and set mechanisms for how these rights would be protected and enforced.
Each regulation also carries with it fines, fees, and legal measures for non-compliance. These can be substantial. And if that’s not enough, there’s an ever-increasing consumer demand for websites that prioritize privacy and security. Consider these statistics:
- 82% of Americans surveyed say they are concerned about the security of their online data
- 79% of adults claim they are very or somewhat worried about how companies use the data they collect about them
- 63% of Americans believe they understand very little or nothing at all about privacy laws and regulations that are intended to protect their data
How Can Developers Implement These Laws?
Privacy by Design is Critical for Websites
Under GDPR, web developers are required to adopt the Privacy by Design framework, which is a multi-point methodology intended to standardize data protection measures.
Building privacy into websites shouldn’t happen at the end stages. It should start with how the websites are conceptualized in the first place. Here are points to prioritize:
- Minimize that data you’re collecting and pseudonymize it to protect data privacy
- Are you capturing consent? How? Where?
- Integrating security measures to protect data — anytime you capture data or implement a third party product, a security risk is born.
- Knowing where you’re introducing privacy and data sharing notices
- Implement just-in-time notices to provide consumers transparency and build trust
- Giving your users the opportunity to manage their personal data
Let’s look at these a little more closely…
Data Minimization is the Goal
Data minimization is an important principle embedded in GDPR. Data minimization itself is a pretty straightforward concept: organizations should limit how much personal data they collect and only process the information necessary to accomplish their business purposes. Once the data is no longer useful, it should be deleted.
For web developers, this means several things. When it comes to building websites, forms, cookies, and other methods should only ask for essential information. For example, if you are creating a pop-up to collect email addresses, don’t ask for their location unless it’s relevant to the email list and better serving their needs.
How and Where Do You Introduce Privacy Policies and Notices?
Let’s say you take data minimization seriously. That’s great! Now you need to put those data collection practices into words and share them with your customers.
Privacy policies and notices are a big part of both GDPR and CCPA. Both the CCPA and the GDPR mandate that your privacy policy detail why you’re collecting information and how it will be used, as well as what the individual’s rights are and how they can exercise them.
CCPA takes a slightly different angle, requiring privacy policies to disclose if the business sells personal data and what third parties have access to the data. CCPA also dictates that privacy policies and notices are current, updated at least annually. (Nota bene: GDPR also asks for updated privacy documents, but doesn’t specify frequency.)
How does this translate from policy into web development?
- If you’re collecting data to improve user experience, allow for targeted ads, or sharing information with third-parties, this information will need to be included in a privacy notice. Remember, CCPA works with a broad definition of selling data, so you may need to account for a “Do Not Sell” link on your home page.
- Considering using data beyond these purposes? Plan to obtain explicit user consent for each additional purpose.
- What’s your plan for the data after the user gives it to you? Where is it stored? Who has access to it? How long are you keeping it? These are all questions that a website developer should consider, and that needs to go into a privacy notice.
Just-in-Time Notices for Transparency and Trust
Part of Privacy by Design is the use of individual components of your website to create transparency and support compliance. From a development and design perspective, this means you should always be looking for ways to communicate the hows and whys of data collection.
Yes, your privacy policies and notices aid in this, but going beyond these pieces is important. Customers recognize when businesses go the extra mile for them, after all.
So consider implementing just-in-time notices at points where users enter their information. These notices are a chance to share your data collection practices with your users. It’s transparent! It’s open! It aids in consumer awareness!
Keep Users in the Loop
Want to win over your customers? Make it as easy as possible for them to manage their personal data and how it’s being used. This starts with making sure they are aware of why you’re requesting their information and how you’re planning on using it for the website. You should also:
- Get user consent — clear and unambiguous user consent — prior to gathering any data at all. This includes cookies.
- Don’t pre-tick boxes for consent. Just don’t. (It’s bad practice AND it’s against GDPR.)
- Link to all legal documents on the site. Users should be required to agree to them before using the service.
- Want to send marketing communications like email newsletters to your customers? Make sure they agree to this. Expressly.
One helpful tool for keeping users in the loop is a marketing preference center. A marketing preference center allows users easy access to their information. From there, they can manage, edit, and delete their information at their discretion.
Bonus? A marketing preference center is an excellent point at which to communicate a business’ commitment to privacy. While users will pick up this through all the discrete elements of privacy on your website, putting it all into one hub that also allows users control over their data really reinforces this message.
Remember, it’s not just on the consumer to manage their data. Web developers should commit to managing the data in their systems. This means they should:
- Maintain accurate and clean records of users’ data consent preferences
- Send regular reminders to users to update their personal information in your system
- If a user deletes their account, promptly delete all of their personal information
- If your client goes out of business or is sold, they should delete all personal information in their system
Make it User Friendly
A final point: making your websites user friendly is important regardless of privacy compliance. Users expect websites that don’t make them think deeply about, or worry about, their privacy. Make it accessible and easy. Don’t make people figure it out on their own.
Give them value for sharing their data
Your users don’t have to share their data. They’re choosing to. So in exchange for their personal information, make sure you’re using it to provide a user-friendly website. Offer them a secure, enjoyable experience.
But don’t ask for more than you need
Let’s loop back around to this point again. While consumer data can help you build a better website, don’t plan your websites around it and don’t demand data to create a good experience.
Usability, web design, and website security; all of these things benefit from consumer data. But privacy laws should always guide how any personal data is collected and used, and respect for consumers’ individual rights, and honoring their privacy should be top-of-mind for web developers.
Featured image via Pexels.