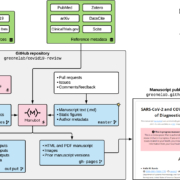
de développement et d’exploitation.
La DevSecOps moderne offre une intégration sécurisée des processus de développement et d’exploitation pour un flux de travail plus fluide et plus sûr.
Rapport de tendances sur la sécurité des entreprises DZone 2023
L’architecture DevSecOps est un moyen de résoudre les problèmes liés aux méthodologies traditionnelles de développement logiciel, en particulier la séparation entre les équipes de développement et de sécurité. Cette séparation entraîne souvent la découverte de vulnérabilités de sécurité tard dans le cycle de développement, ce qui entraîne des retards et des réaménagements coûteux. DevSecOps vise à briser ces silos en intégrant des pratiques de sécurité dans l’ensemble du cycle de développement logiciel (SDLC), de la planification et du codage à la mise en œuvre et à la surveillance.
DevSecOps est une approche holistique qui permet aux équipes de développement et de sécurité de travailler ensemble pour intégrer la sécurité dans le développement logiciel. Les principes fondamentaux de DevSecOps sont l’automatisation, la collaboration et la responsabilisation. L’automatisation permet aux équipes de développement et de sécurité de créer des processus et des outils qui intègrent la sécurité dans le processus de développement. La collaboration permet aux équipes de travailler ensemble pour résoudre les problèmes et partager les connaissances. La responsabilisation permet aux membres des équipes de développement et de sécurité d’être responsables des résultats. Enfin, l’utilisation d’une architecture DevSecOps permet aux organisations de réduire leurs risques en matière de sécurité et d’améliorer leurs processus de développement logiciel.